
Menace actors behind the Akira ransomware group have extorted roughly $42 million in illicit proceeds after breaching the networks of greater than 250 victims as of January 1, 2024.
“Since March 2023, Akira ransomware has impacted a variety of companies and demanding infrastructure entities in North America, Europe, and Australia,” cybersecurity businesses from the Netherlands and the U.S., together with Europol’s European Cybercrime Centre (EC3), mentioned in a joint alert.
“In April 2023, following an preliminary deal with Home windows programs, Akira menace actors deployed a Linux variant focusing on VMware ESXi digital machines.”
The double-extortion group has been noticed utilizing a C++ variant of the locker within the early levels, earlier than shifting to a Rust-based code as of August 2023. It is value noting that the e-crime actor is totally totally different from the Akira ransomware household that was energetic in 2017.
Preliminary entry to focus on networks is facilitated by the use of exploiting identified flaws in Cisco home equipment (e.g., CVE-2020-3259 and CVE-2023-20269).
Alternate vectors contain the usage of Distant Desktop Protocol (RDP), spear-phishing, legitimate credentials, and digital non-public community (VPN) providers missing in multi-factor authentication (MFA) protections.

Akira actors are additionally identified to leverage numerous methods to arrange persistence by creating a brand new area account on the compromised system, in addition to evade detection by abusing the Zemana AntiMalware driver to terminate antivirus-related processes through what’s known as a Carry Your Personal Susceptible Driver (BYOVD) assault.
To assist in privilege escalation, the adversary depends on credential scraping instruments like Mimikatz and LaZagne, whereas Home windows RDP is utilized to maneuver laterally inside the sufferer’s community. Knowledge exfiltration is achieved by way of FileZilla, WinRAR, WinSCP, and RClone.
“Akira ransomware encrypts focused programs utilizing a hybrid encryption algorithm that mixes Chacha20 and RSA,” Pattern Micro mentioned in an evaluation of the ransomware revealed in October 2023.
“Moreover, the Akira ransomware binary, like most trendy ransomware binaries, has a function that permits it to inhibit system restoration by deleting shadow copies from the affected system.”
Blockchain and supply code knowledge means that Akira ransomware group is probably going affiliated with the now-defunct Conti ransomware gang. A decryptor for Akira was launched by Avast final July, however it’s extremely doubtless the shortcomings have since been plugged.

Akira’s mutation to focus on Linux enterprise environments additionally follows related strikes by different established ransomware households akin to LockBit, Cl0p, Royal, Monti, and RTM Locker.
LockBit’s Struggles to Come Again
The disclosure comes as Pattern Micro revealed that the sweeping regulation enforcement takedown of the prolific LockBit gang earlier this February has had a major operational and reputational affect on the group’s means to bounce again, prompting it to put up previous and pretend victims on its new knowledge leak web site.
“LockBit was one of the vital prolific and extensively used RaaS strains in operation, with doubtlessly a whole bunch of associates, together with many related to different outstanding strains,” Chainalysis famous in February.
The blockchain analytics agency mentioned it uncovered cryptocurrency trails connecting a LockBit administrator to a journalist primarily based in Sevastopol often known as Colonel Cassad, who has a historical past of soliciting donations for Russian militia group operations within the sanctioned jurisdictions of Donetsk and Luhansk following the onset of the Russo-Ukrainian battle in 2022.
It is value stating that Cisco Talos, in January 2022, linked Colonel Cassad (aka Boris Rozhin) to an anti-Ukraine disinformation marketing campaign orchestrated by the Russian state-sponsored group often known as APT28.
“Following the operation, LockBitSupp [the alleged leader of LockBit] seems to be trying to inflate the obvious sufferer rely whereas additionally specializing in posting victims from nations whose regulation enforcement businesses participated within the disruption,” Pattern Micro mentioned in a current deep dive.

“That is probably an try to bolster the narrative that it might come again stronger and goal these accountable for its disruption.”
In an interview with Recorded Future Information final month, LockBitSupp acknowledged the short-term decline in income, however promised to enhance their safety measures and “work so long as my coronary heart beats.”
“Status and belief are key to attracting associates, and when these are misplaced, it is more durable to get individuals to return. Operation Cronos succeeded in putting in opposition to one aspect of its enterprise that was most essential: its model,” Pattern Micro said.
Agenda Returns with an Up to date Rust Model
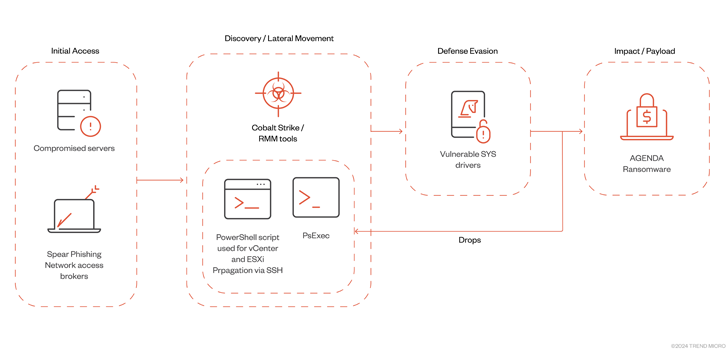
The event additionally follows the Agenda ransomware group’s (aka Qilin and Water Galura) use of an up to date Rust variant to contaminate VMWare vCenter and ESXi servers by way of Distant Monitoring and Administration (RMM) instruments and Cobalt Strike.
“The Agenda ransomware’s means to unfold to digital machine infrastructure exhibits that its operators are additionally increasing to new targets and programs,” the cybersecurity firm mentioned.
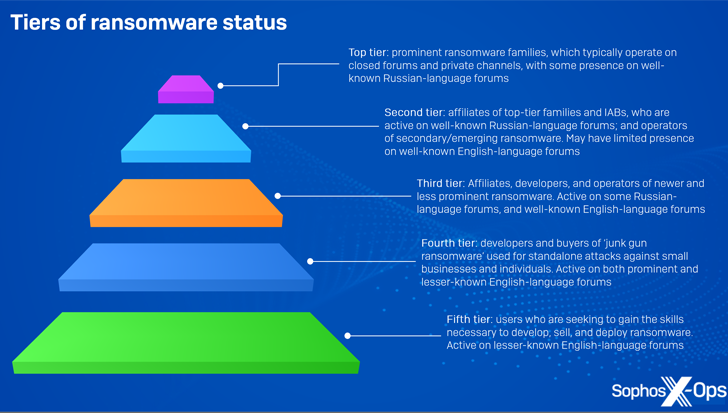
At the same time as a recent crop of ransomware actors continues to energise the menace panorama, it is also turning into clearer that “crude, low cost ransomware” bought on the cybercrime underground is being put to make use of in real-world assaults, permitting lower-tier particular person menace actors to generate vital revenue with out having to be part of a well-organized group.
Apparently, a majority of those varieties can be found for a single, one-off value ranging from as little as $20 for a single construct, whereas just a few others akin to HardShield and RansomTuga are provided at no additional price.
“Away from the advanced infrastructure of recent ransomware, junk-gun ransomware permits criminals to get in on the motion cheaply, simply, and independently,” Sophos mentioned, describing it as a “comparatively new phenomenon” that additional lowers the price of entry.
“They will goal small corporations and people, who’re unlikely to have the sources to defend themselves or reply successfully to incidents, with out giving anybody else a lower.”

